Provide Comprehensive Compliance Assessments
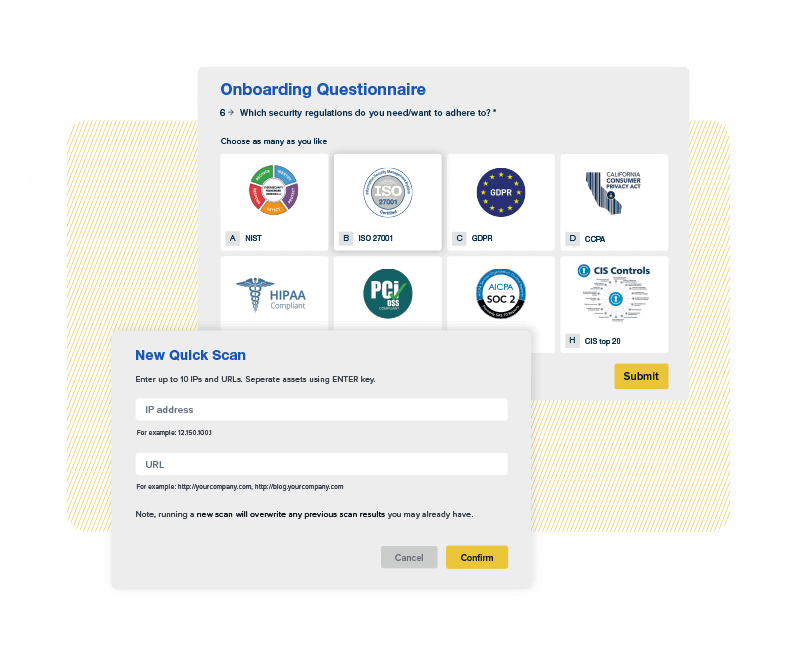
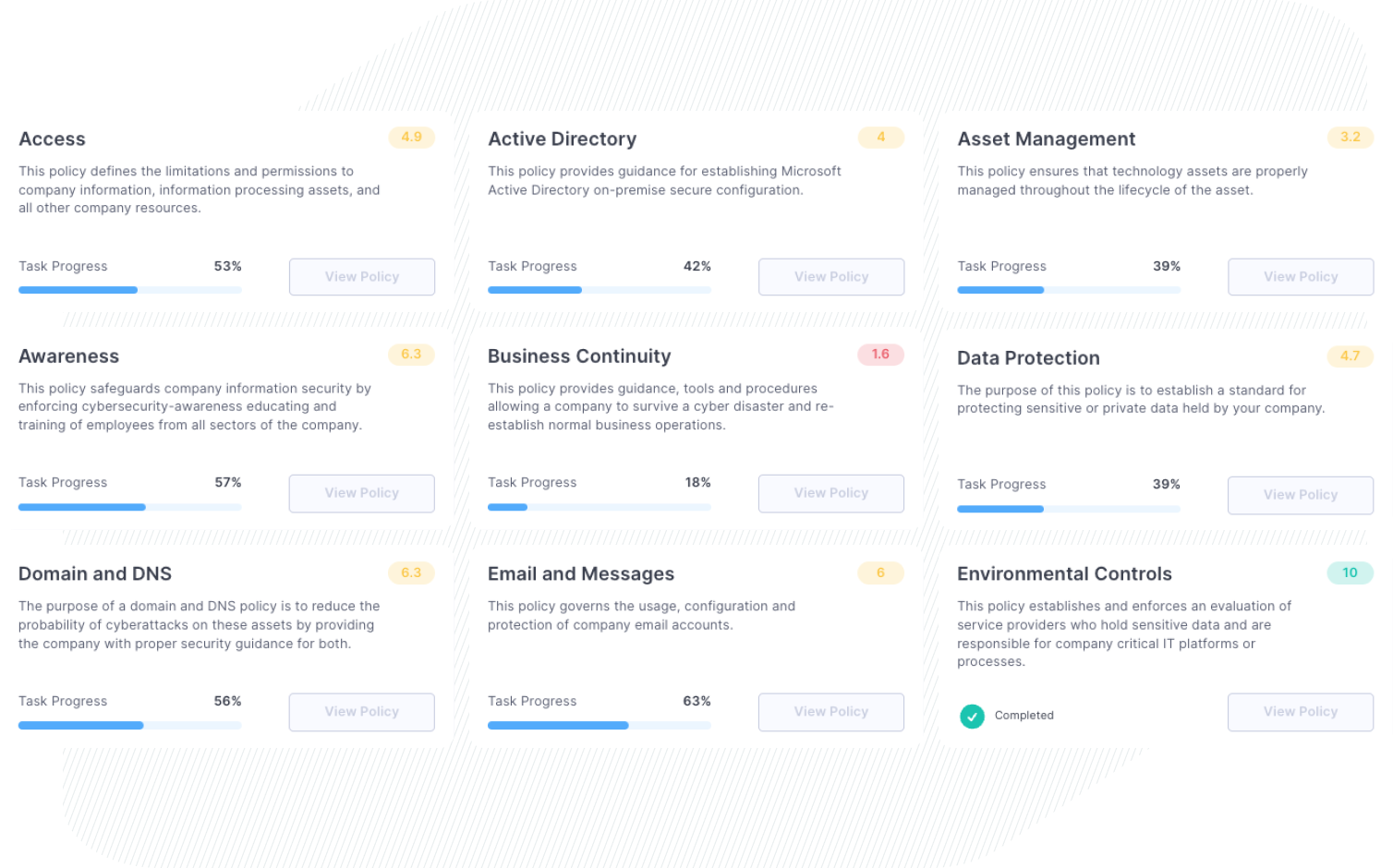
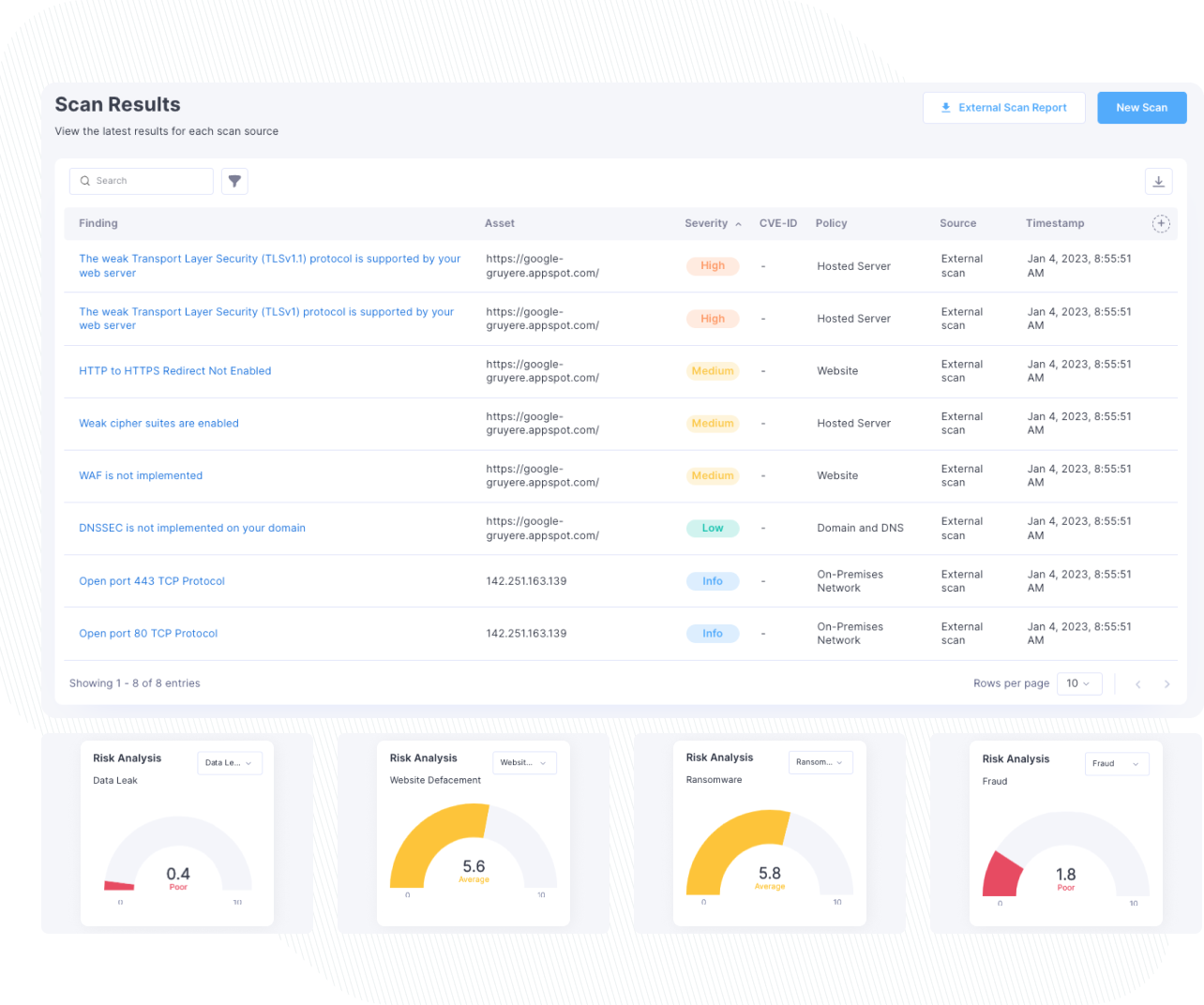
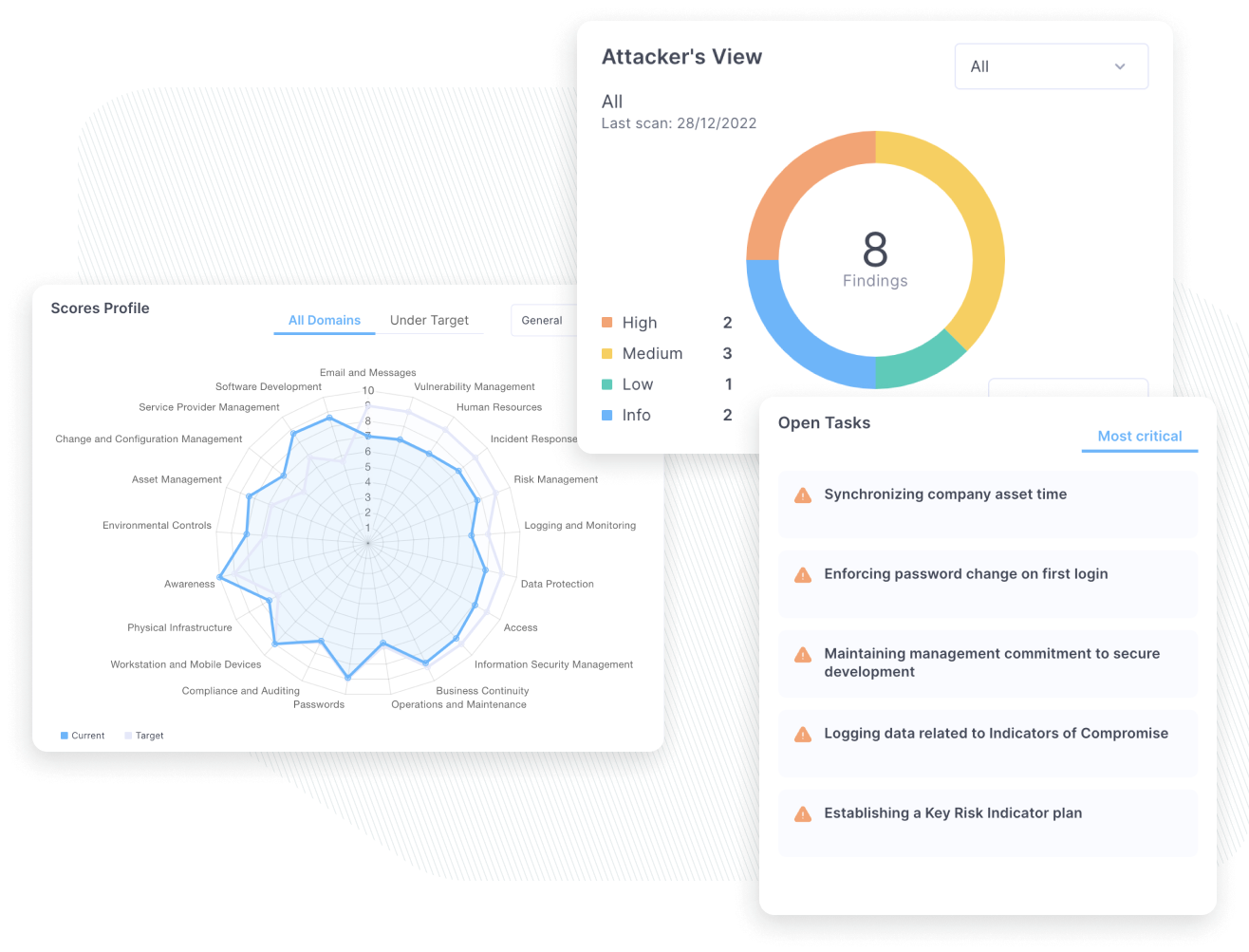
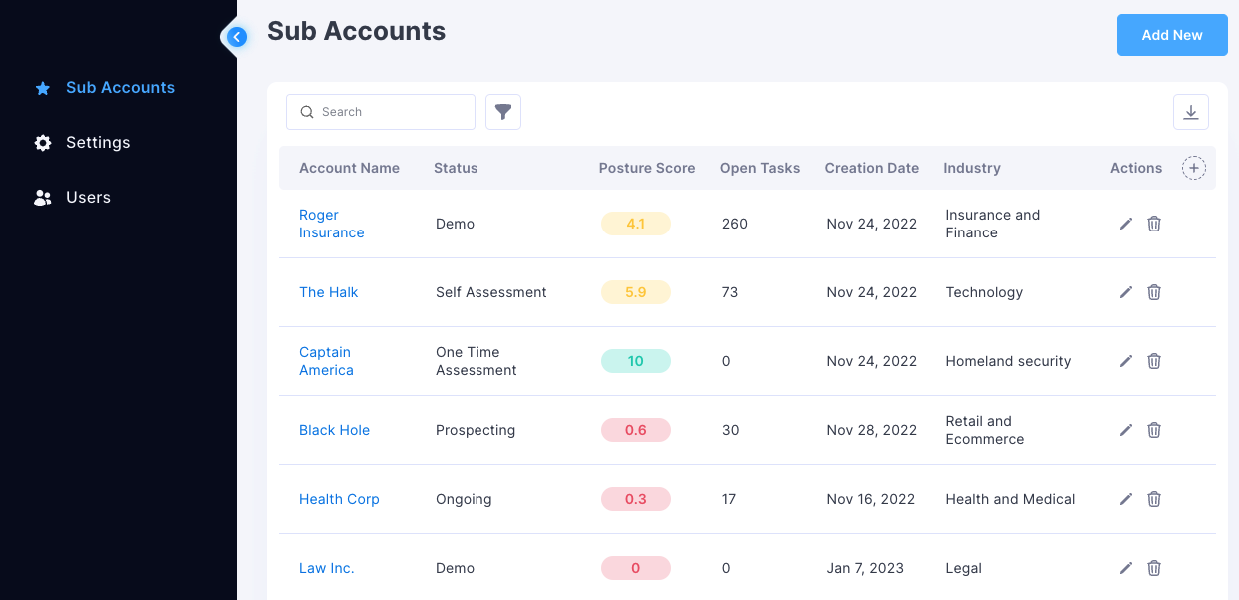
Leveraging Cynomi’s AI-powered, automated vCISO platform, managed service providers and consulting firms can offer comprehensive compliance assessments for multiple frameworks such as ISO27001 or CISv8, delivering automatically-generated tailored policies and strategic remediation plans with prioritized tasks to each client.
Request a DemoSimplify Assessment
Automate the manual, time-consuming work of compliance assessments to save time and allow focusing on closing compliance gaps
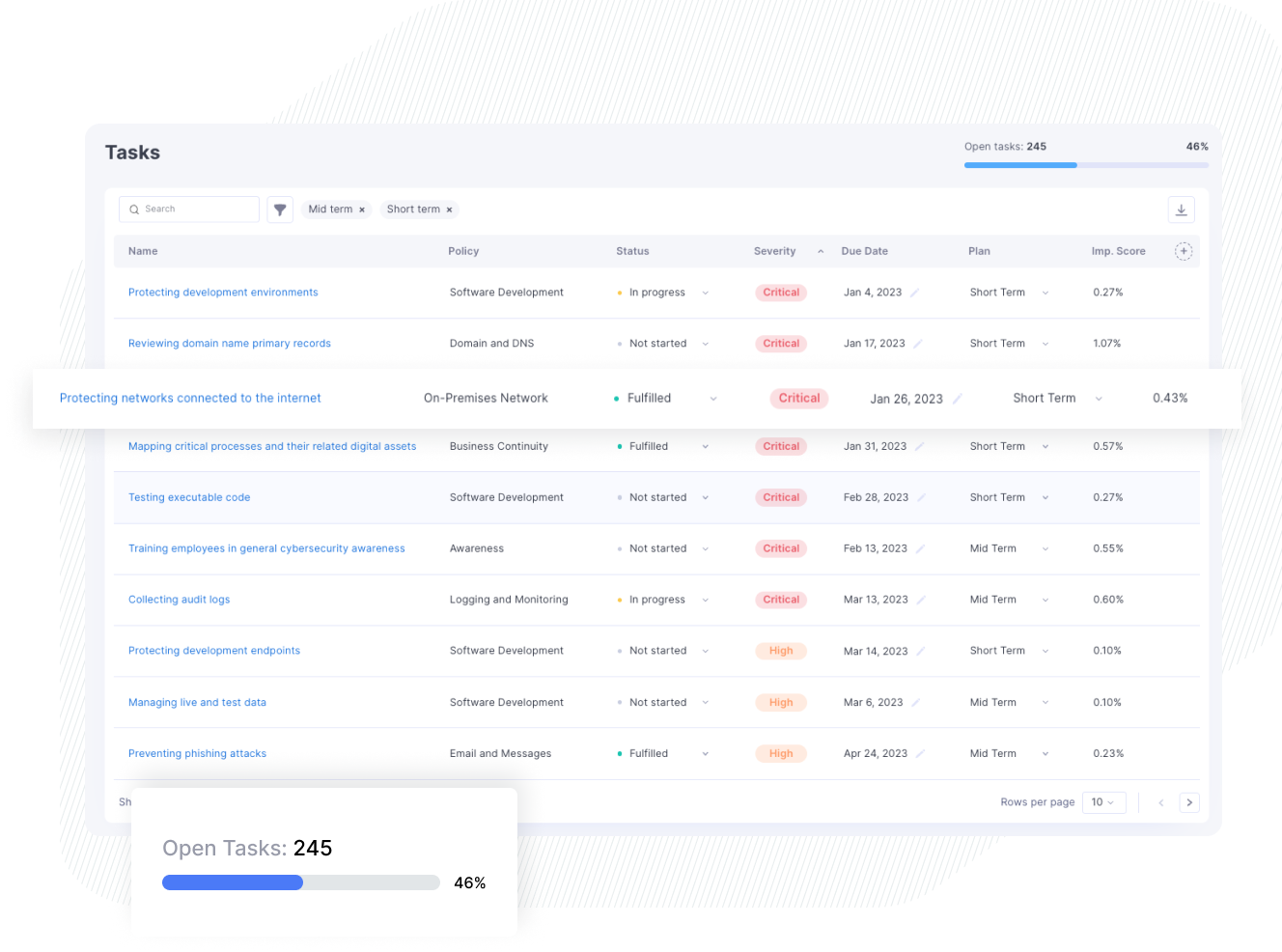
Expedite Remediation
Use Cynomi's automatically-generated remediation plan to eliminate the planning hassle and start working on the most effective tasks
Stand Out, Grow Revenue
Offer comprehensive compliance assessments that stand out in the market without the need to develop in-house expertise or scale your existing resources